Why Post-Launch Audits Define Success
The excitement of a website launch often overshadows critical risks. When a new platform fails shortly after deployment, the cause is often poor Post-Launch Security Audit procedures. Security debt is accumulated in the rush to meet deadlines. This can lead to costly downtime or, worse, a devastating data breach.
A systematic audit transforms risk into resilience. It is an indispensable step in any successful Digital Transformation Security strategy. This 47-point checklist is your guide. Use it to lock down your digital asset and establish long-term trust. We cover everything from server setup to complex code vulnerabilities.
A successful digital product is less about the launch fanfare and more about the ongoing, uncompromised commitment to security. The audit phase is where the real governance begins.”
– Sociazy Cybersecurity Director.
Domain 1: Infrastructure and Network Hardening (Points 1–12)
The server environment is the first line of defense. Weak configuration here exposes your entire application. This domain focuses on the physical and virtual perimeter.
Cloud & Server:
- Are unnecessary services and daemons disabled on the server?
- Is the Operating System (OS) patched to the latest stable version?
- Are default credentials for cloud consoles and servers fully replaced?
- Is SSH/RDP access secured via key pairs or strong, non-default ports?
Network Perimeter:
- Is a high-quality Web Application Firewall (WAF) actively filtering traffic?
- Is the load balancer configured to drop non-HTTPS requests?
- Are all administrative endpoints restricted to internal IP ranges?
- Has the SSL/TLS configuration been verified for compliance and strength?
Separation and Zoning:
- Are the database and application servers placed in separate, restricted network zones?
- Is the staging environment fully isolated from the production environment?
- External Link: Consult the Center for Internet Security (CIS) Benchmarks for optimal server hardening guidelines.
- Are adequate resources allocated to handle peak traffic without crashing the server?
Domain 2: Application Code Integrity (Points 13–28)
Most security weaknesses stem from insecure coding practices. This section targets the top vulnerabilities identified by experts.
Input Handling:
- Is all user-supplied data subjected to strict server-side validation?
- Are parameterized statements used exclusively for database interactions (preventing SQL injection)?
- Is output encoding applied to prevent Cross-Site Scripting (XSS)?
Dependencies and Libraries:
- Is a continuous scanner used to check third-party libraries for known vulnerabilities (CVEs)?
- Are all unnecessary application features or modules removed or disabled?
- Is the use of server-side includes or direct file access strictly managed?
Error Management:
- Do custom error pages suppress revealing technical details like stack traces or server paths?
- Are all security-related events logged centrally for monitoring?
- Real-world Example/Case: A major retail site’s launch failed due to an unpatched third-party library. The resulting code vulnerability exposed customer data within 48 hours.
APIs and Business Logic:
- Are rate limits applied to all external and internal API calls?
- Are object-level authorization checks performed on all data requests?
- Is the application resilient against common Business Logic Flaws?
- Internal Link: Deploy automated checks using tools.
- Is the Content Security Policy (CSP) headers correctly configured and enforced?
- Are uploaded files stored outside the web root and checked for executable content?
- Are HTTP security headers (HSTS, X-Content-Type-Options) correctly applied?
Domain 3: Authentication and Access Control (Points 29–37)
Securing access is fundamental to any Post-Launch Security Audit. Weak user management is an open door to attackers.
User Credentials:
- Are user passwords hashed using strong, slow algorithms (e.g., Argon2 or bcrypt)?
- Is Multi-Factor Authentication (MFA) mandatory for all privileged users?
- Are strict password policies enforced (complexity, rotation)?
Session Management:
- Are sessions regenerated upon successful login and privilege escalation?
- Are session tokens set to expire after a short period of inactivity?
- Are cookies secured with the
HttpOnlyandSecureflags?
Permissions:
- Is Role-Based Access Control (RBAC) correctly implemented for all system functions?
- Is the principle of Least Privilege applied to all users, internal and external?
- Are user input parameters strictly validated against expected permission levels?
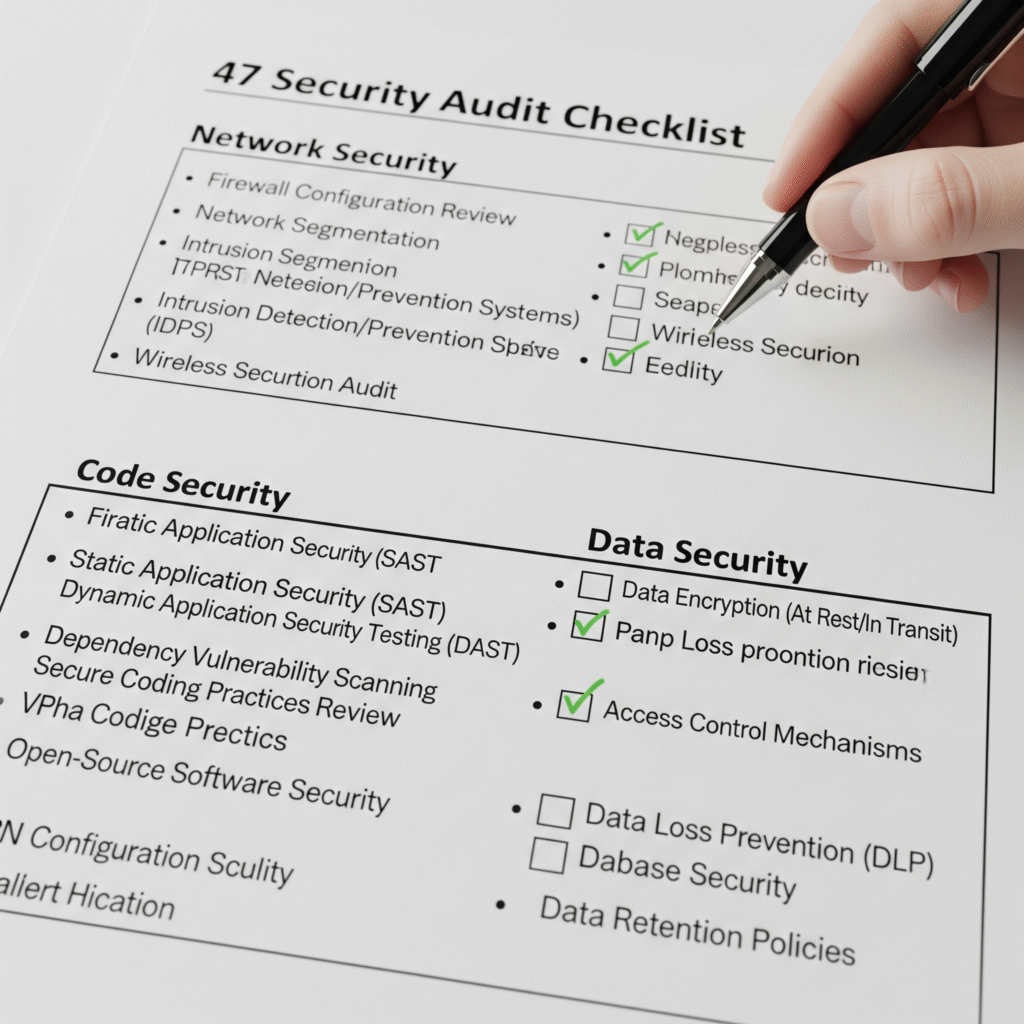
Domain 4: Compliance, Monitoring, and Recovery (Points 38–47)
Security is an ongoing operational commitment, not a one-time setup. This final domain ensures long-term viability and recovery capability.
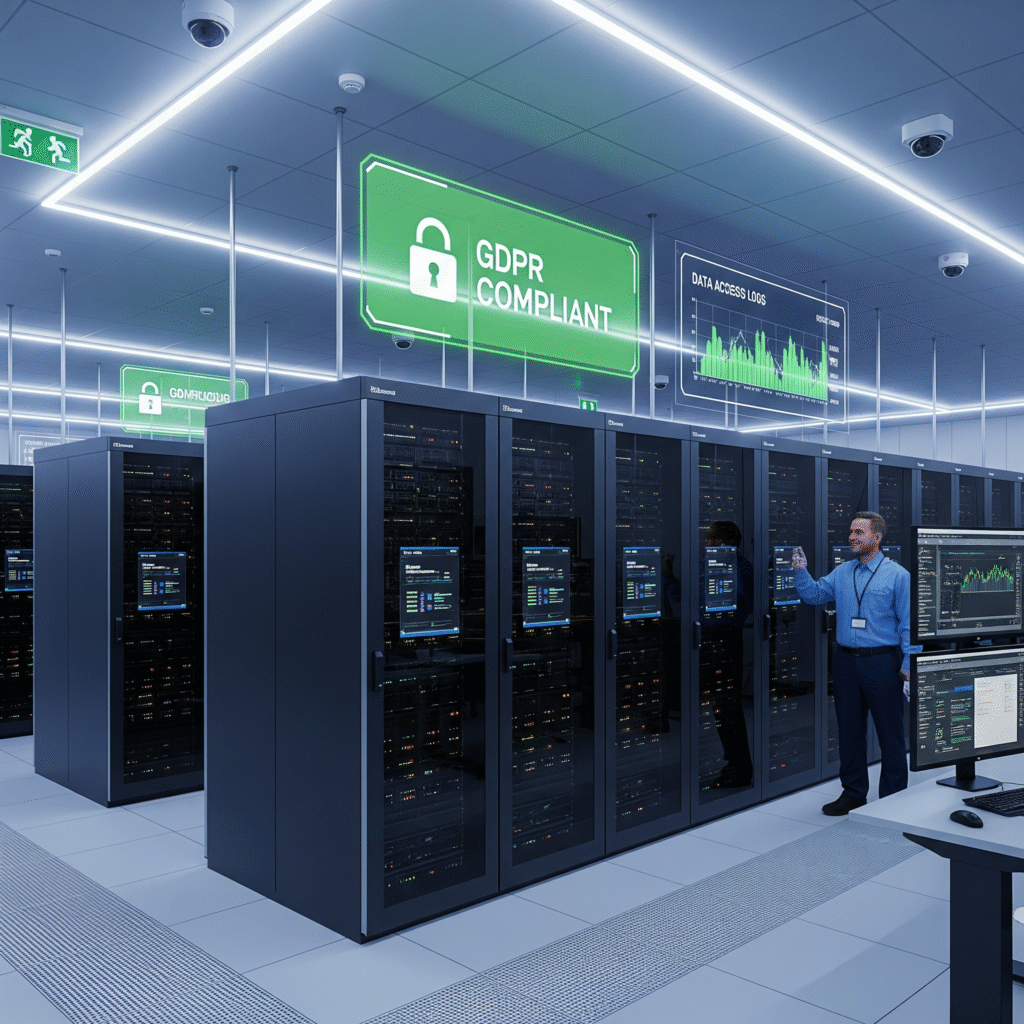
Data and Privacy:
- Is all sensitive data encrypted both at rest and in transit?
- Is data retention compliant with relevant laws (GDPR, CCPA, etc.)?
- Current/Evergreen Statistic: Studies show that organizations that adopt a high degree of security automation experience recovery costs up to $3 million lower than those without it.
Logging and Monitoring:
- Is comprehensive logging enabled for all security-relevant events?
- Is a Security Information and Event Management (SIEM) system actively monitoring logs for anomalies?
- Are alerts configured for failed login attempts, unusual traffic patterns, and critical server status?
Recovery and Readiness:
- Has a clear Incident Response Plan (IRP) been documented and communicated?
- Are reliable, tested backups performed daily and stored securely offsite?
- Has the Disaster Recovery (DR) process been tested recently and successfully?
- Internal Link: Learn how to build a robust IRP in our guide.
Conclusion: From Failure to Fortified
Launching a website is a significant digital transformation. Allowing it to fail due to preventable security gaps is a costly mistake. By utilizing this rigorous 47-point Website Vulnerability Checklist, you move past quick fixes. You build a foundation of secure resilience. This systematic approach—covering infrastructure, code, data, and compliance—ensures your platform remains stable, trustworthy, and compliant for years to come.
Ready to Transform Your All Industries Strategy?
Stop wondering and start transforming. Contact Sociazy’s expert team today for a no-obligation consultation on how we can solve your specific All Industries challenges.
Engagement Prompt: What’s the biggest internal challenge your team faces when enforcing security policies after a major launch?